

How Malicious Android Apps Slip Into Disguise
source link: https://krebsonsecurity.com/2023/08/how-malicious-android-apps-slip-into-disguise/
Go to the source link to view the article. You can view the picture content, updated content and better typesetting reading experience. If the link is broken, please click the button below to view the snapshot at that time.

How Malicious Android Apps Slip Into Disguise – Krebs on Security

Researchers say mobile malware purveyors have been abusing a bug in the Google Android platform that lets them sneak malicious code into mobile apps and evade security scanning tools. Google says it has updated its app malware detection mechanisms in response to the new research.
At issue is a mobile malware obfuscation method identified by researchers at ThreatFabric, a security firm based in Amsterdam. Aleksandr Eremin, a senior malware analyst at the company, told KrebsOnSecurity they recently encountered a number of mobile banking trojans abusing a bug present in all Android OS versions that involves corrupting components of an app so that its new evil bits will be ignored as invalid by popular mobile security scanning tools, while the app as a whole gets accepted as valid by Android OS and successfully installed.
“There is malware that is patching the .apk file [the app installation file], so that the platform is still treating it as valid and runs all the malicious actions it’s designed to do, while at the same time a lot of tools designed to unpack and decompile these apps fail to process the code,” Eremin explained.
Eremin said ThreatFabric has seen this malware obfuscation method used a few times in the past, but in April 2023 it started finding many more variants of known mobile malware families leveraging it for stealth. The company has since attributed this increase to a semi-automated malware-as-a-service offering in the cybercrime underground that will obfuscate or “crypt” malicious mobile apps for a fee.
Eremin said Google flagged their initial May 9, 2023 report as “high” severity. More recently, Google awarded them a $5,000 bug bounty, even though it did not technically classify their finding as a security vulnerability.
“This was a unique situation in which the reported issue was not classified as a vulnerability and did not impact the Android Open Source Project (AOSP), but did result in an update to our malware detection mechanisms for apps that might try to abuse this issue,” Google said in a written statement.
Google also acknowledged that some of the tools it makes available to developers — including APK Analyzer — currently fail to parse such malicious applications and treat them as invalid, while still allowing them to be installed on user devices.
“We are investigating possible fixes for developer tools and plan to update our documentation accordingly,” Google’s statement continued.
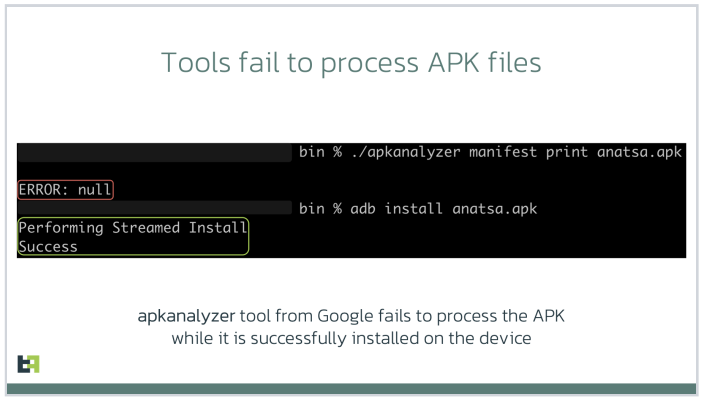
Image: ThreatFabric.
According to ThreatFabric, there are a few telltale signs that app analyzers can look for that may indicate a malicious app is abusing the weakness to masquerade as benign. For starters, they found that apps modified in this way have Android Manifest files that contain newer timestamps than the rest of the files in the software package.
More critically, the Manifest file itself will be changed so that the number of “strings” — plain text in the code, such as comments — specified as present in the app does match the actual number of strings in the software.
One of the mobile malware families known to be abusing this obfuscation method has been dubbed Anatsa, which is a sophisticated Android-based banking trojan that typically is disguised as a harmless application for managing files. Last month, ThreatFabric detailed how the crooks behind Anatsa will purchase older, abandoned file managing apps, or create their own and let the apps build up a considerable user base before updating them with malicious components.
ThreatFabric says Anatsa poses as PDF viewers and other file managing applications because these types of apps already have advanced permissions to remove or modify other files on the host device. The company estimates the people behind Anatsa have delivered more than 30,000 installations of their banking trojan via ongoing Google Play Store malware campaigns.
Google has come under fire in recent months for failing to more proactively police its Play Store for malicious apps, or for once-legitimate applications that later go rogue. This May 2023 story from Ars Technica about a formerly benign screen recording app that turned malicious after garnering 50,000 users notes that Google doesn’t comment when malware is discovered on its platform, beyond thanking the outside researchers who found it and saying the company removes malware as soon as it learns of it.
“The company has never explained what causes its own researchers and automated scanning process to miss malicious apps discovered by outsiders,” Ars’ Dan Goodin wrote. “Google has also been reluctant to actively notify Play users once it learns they were infected by apps promoted and made available by its own service.”
The Ars story mentions one potentially positive change by Google of late: A preventive measure available in Android versions 11 and higher that implements “app hibernation,” which puts apps that have been dormant into a hibernation state that removes their previously granted runtime permissions.
Recommend
-
 39
39
Testing can be simple. In fact, it is simple. Well, it is simple until impurities slip in. Code that would be easy to test becomes a nightmare as soon as you get impure data (like date...
-
 39
39
Suppose you have an application that manages employees or users. You need to make a simple function that will create a new employee, but you want to make sure that the employee always contains certain fields and will have...
-
 6
6
Your Life Problems are Really Learning Challenges in Disguise 原文地址:https://www.scotthyoung.com/blog/2019/05/10/life-problems-are-learni...
-
 5
5
ConversationPR training is sometimes a blessing in disguise for them. But some engineers don't take to it as well as others, that's why comms teams are reluctant to put engineers in front of press
-
 6
6
disguise 推出元宇宙解决方案部门,实现更高水平的扩展现实体验2022/05/26 14:37|
-
 15
15
iPhone 14 Pro and iPhone 14 Pro Max pre-order delivery dates quickly slip into October Friday, September 9, 2022 12:50 pm
-
 5
5
InternetAntivaxxers Are Using the Carrot Emoji to Disguise Talking About the JabAntivaxxers have been using the vegetable em...
-
 6
6
The new iPad’s USB-C port is really a Lightning port in disguise It’s like Lightning never left. By
-
 7
7
新浪VR > 正文页 Snap 与 Disguise 合作,推出用于万圣节服装的 AR 试穿滤镜...
-
 10
10
This 500HP Lamborghini Miura Is Actually A Pontiac Fiero In Disguise
About Joyk
Aggregate valuable and interesting links.
Joyk means Joy of geeK